Next gen blockchain intelligence
Let's re-define investigation software together.
55+
Successful interviews
170+
LinkedIn followers
20+
Expert consultations
Summary
Table of contents
Business proposal
Emerging tech to tackle a growing problem
Market opportunity

PAM
$11.9 B
Global financial losses due to crypto scams
TAM
$2.90 B
Global crypto compliance and analytics market
SAM
$2.37 B
US crypto investigation market
SOM
$119 M
US Market size for ninepointthree
Long-term market share
Competitor landscape




Product
Accessible to small/medium firms
Pricing flexibility
Data visibility and smart UI
AI evidence generation
Learning curve
High
High
High
High
Low
AI-powered automatic tracing
Cross-chain tracing
Free trial
Limited
Demixing
Case monitoring with alerts
Variety of background tracing alert types
Chains available
335+
100+
15
10+
20+
Company
Number of employees
750
200
<20
<20
N/A
Market share
36.3%
24.3%
<4.6%
<4.6%
N/A
Established year
2018
2013
2018
2021
2025
Location of HQ
USA
UK
Singapore
Austria
USA
Business roadmap

Seed (3 Months)
Jul 2026 - Sept 2026
San Francisco & NY, USA
+ International conference attendance
+ Working with sponsor users
+ Targeted online adverts
0
Early stage (1 Year)
Oct 2026 - Sept 2027
USA
International conference attendance
Working with sponsor users
+ Influential voice partnerships
Targeted online adverts
0
Accessing bigger players (1 Year)
Oct 2027 - Sept 2028
USA
Europe
1 direct B2B salesperson
Growth stage (1 Year+)
Oct 2028+
USA
Europe
Singapore
International conference attendance
Influential voice partnerships
Large law firm partnerships
Targeted online adverts
2 direct B2B salespeople
Financial projections
Below are details of ninepointthree's 5-yr financial projections and funding strategies for sustainable cash flow. Many of the business's de-risking activities shown on this page informed the calculation assumptions made.
Why launch in the US?


Number of direct ninepointthree users is ~10x greater (as of 2026)
Larger number of blockchain tech conferences enabling rapid customer reach
High-value accelerators and grants focused on funding blockchain innovation that we are looking to apply for
Legal system is more amenable to AI automation in evidence generation
Few independent crypto investigators (mainly exist as part of large law firms)
Limited number of conferences at the scale we need for effective customer acquisition
Blockchain & tech innovation grants are not high-value enough for our cash flow projections
Legal system not yet open to AI integration
Experiments
Validated across our four key risks
User - Desirability
Are users willing to pay for our product?
Assumption | Experiment | Key takeaway | Next steps
Assumption 1
Do users value our features?
Experiment: Expert interview & concept testing
We conducted one-hour deep-dive sessions with five direct customers to evaluate our core features, identify the most valuable features and identify potential improvements. Feedback was integrated into the high-fidelity prototype. We validated this prototype through a final round of in-person and remote interviews with seven additional users.


Cameron Stark
Power user Blockchain Investigator
Ralph Dahm
Power user Blockchain Investigator

Abubakar Maruf
Casual user
Fraud & Monitoring Analyst

Basil Manoussos
Power user Forensic Scientist

Aleks Rings
Casual user
Forensic Accountant
Feature prioritization: Which one is the most valuable?
After presentation of each key features, here are what customers say about our product.
4
Background Tracing & Notification
Existing solution, can be improved
"It's a good feature, but ETA scan might already be doing this. It could be improved by adding SMS or email alerts that notify you whenever funds are moved out of a monitored wallet."
3
Evidence Bundle Generation
Valuable add-on, reducing workload
"If that can somehow be turned into a big transaction table in the click of a button, that would save me 8 hours per report. That would be huge."
2
Automatic Multipath Tracing
More channels, stronger connections
Reach your audience everywhere with seamless multichannel engagement tailored for growth.
1
Algorithmic Lead Prioritization
Most valuable, must have
"In terms of aiding the actual tracing process through database built on algorithm built on huge sort of data sets is is really, really useful."
Feature requirements: What would make it valuable to you?
For each feature, we drafted a list of requirements based on user feedback, which were prioritized via an effort to impact matrix. The next section showcases how we integrated the feedback.

Users want a clear presentation to see everything mapped out on the UI including the transactions, the clusters, wallets.
The multipath tracing needs to give options to the selection logics like FIFO (first in first out), LIFO (last in first out) to users for them to select the attributions.




Assumption 2
How much are users willing to pay?
Experiment: Van Westendorp pricing interviews
We conducted Van Westendorp method with five potential users across the UK and the US to identify the optimal price point of our platform.

Potential Price Range
Too cheap to be true
Still a good deal
Somewhat expensive
Way too expensive
“You wouldn't want to pay less than a grand for it because we know these software are expensive.”
“You start looking at $1,600 a month for a good price.”
“It's starting to get expensive when you go over $2,000 a month. ”
“Even if it's very expensive software, usually you can try and make it work But there is no way I would go over $4,500 a month. ”
Julie Anne Vos
Crypto Fraud Investigator & Consultant
Chioma Onyekelu
Crypto Compliance & AML Specialist
Andrii Skvortsov
Crypto & Financial Investigator
Julie Cho
Blockchain Investigator




Next steps
We will continue to work with our sponsor users to improve our product and implement the tiered pricing model, including the introduction of on-demand access to premium features for users with high or variable case loads. With the pricing and features defined, we want to understand how to sell it to our potential customers.
GTM - Reachability
Can we acquire the customers and partners needed to access our obtainable market?
Assumption | Experiment | Key takeaway | Next steps
Assumption 1
Are we able to make a significant impression in traditional B2B advertising channels to reach our targeted customer base?
Experiment: LinkedIn traction
We launched the official ninepointthree LinkedIn business page, and then tracked organic reach (impressions), follower growth, and conducted a statistical demographic audit of the professionals engaging with our brand.



organic impressions from initial contents
increase in targeted followers in two weeks
leads obtained from potential partners for sponsorship
Assumption 2
Will influential voices, customers and partners in the US (and international) space validate and advertise our product organically?
Experiment: Influential voices
We conducted targeted outreach and in depth interviews with two industry influential voices to test if they would promote our tool in exchange for free access.
“I could promote it highly and get other people to come to you. Acting as your sales marketing rep in the US.”
—— Ralph Dahm
Blockchain Investigator with a proprietary network of 35,000+ compliance professionals, frequently featured on major news networks.

"The process is simple, I collect the best research tools for crypto and distribute them directly through my repo.”
—— Asharib Ali
Creator of the Curated List of Crypto Research Tools (the 2nd most-starred GitHub repository globally for blockchain intelligence), with an engaged audience of 1.4k developers on GitHub and 13,600+ on LinkedIn.
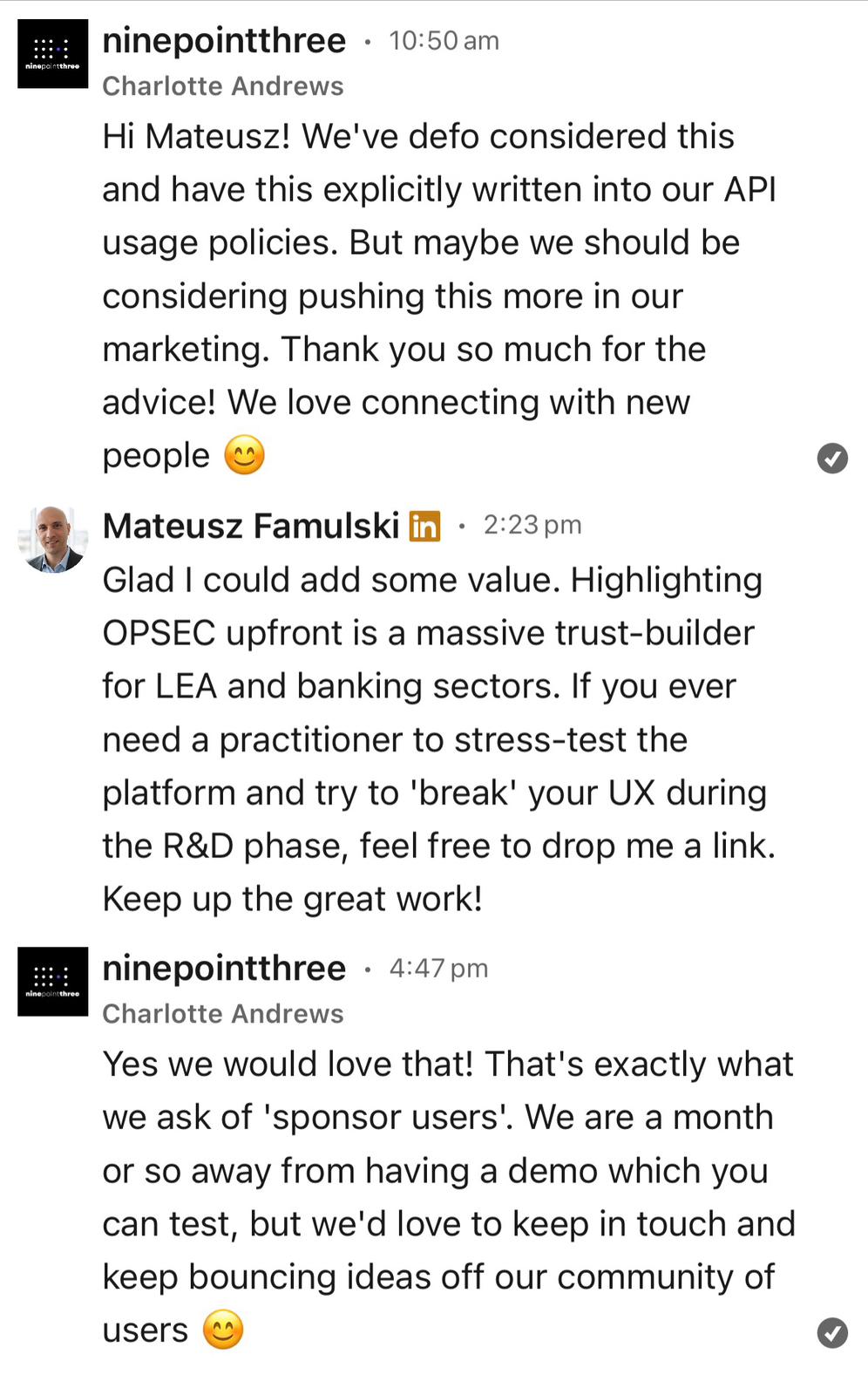
Assumption 3
Are large-scale industry showcasing and networking events are a feasible customer acquisition channel for ninepointthree?
Experiment: In-person conference attendance
We attended the FutureTech Expo 2026, and used this to network with potential customers, compliance partners, and investors, and demonstrated our demo live. We tested the mechanics, costs, and conversion rates of B2B software sales in this cybersecurity space.

Next steps
Continued advertising work on Linkedin and other B2B communication platforms, and continued attendance at large-scale industry conferences. We engaged Key Opinion Leaders (KOLs) as sponsor users by offering access to our closed beta. These experts will safely pressure-test our AI workflows. These collaborations will provide high-trust case studies that will serve as content for our marketing strategy. Now we validated the market potential, our next step is to ensure that the product is feasible.
Technology - Feasibility
Can we build ninepointthree?
Assumption | Experiment | Key takeaway | Next steps
Steps for on-chain forensic investigations

Within our software architecture, the following steps constitute the core of our investigation algorithm, and each is evaluated below.
Assumption 1
Can we get access to on-chain transaction data?
Experiment: Interview with blockchain researcher
"Public blockchains (like Bitcoin and Ethereum) are indeed designed with ledger transparency as a core feature. Transaction data on these chains is publicly viewable, and it is possible to extract data from transactions, retrieve address histories, and analyze transaction flows."
—— Aida Manzano Kharman
Blockchain researcher @ Imperial College London
Assumption 2
Can we track assets across blockchains?
Experiment: Interview with blockchain data engineer
We interviewed an engineer from a competitor companies Iknaio. Our conversation centred on understanding their cross-chain architecture and how they distinguish their capabilities.
"There is no exact way. Each company maintains its own approach to reverse-engineering these protocols. "
—— Michael Fröwis
Head of engineering @ Iknaio
Assumption 3
Is it possible to trace transactions through a mixer?
Experiment: Desk research analysis
We synthesized current academic research and forensic case studies on mixing protocols to examine whether we can integrate demixing methodologies into our tool.
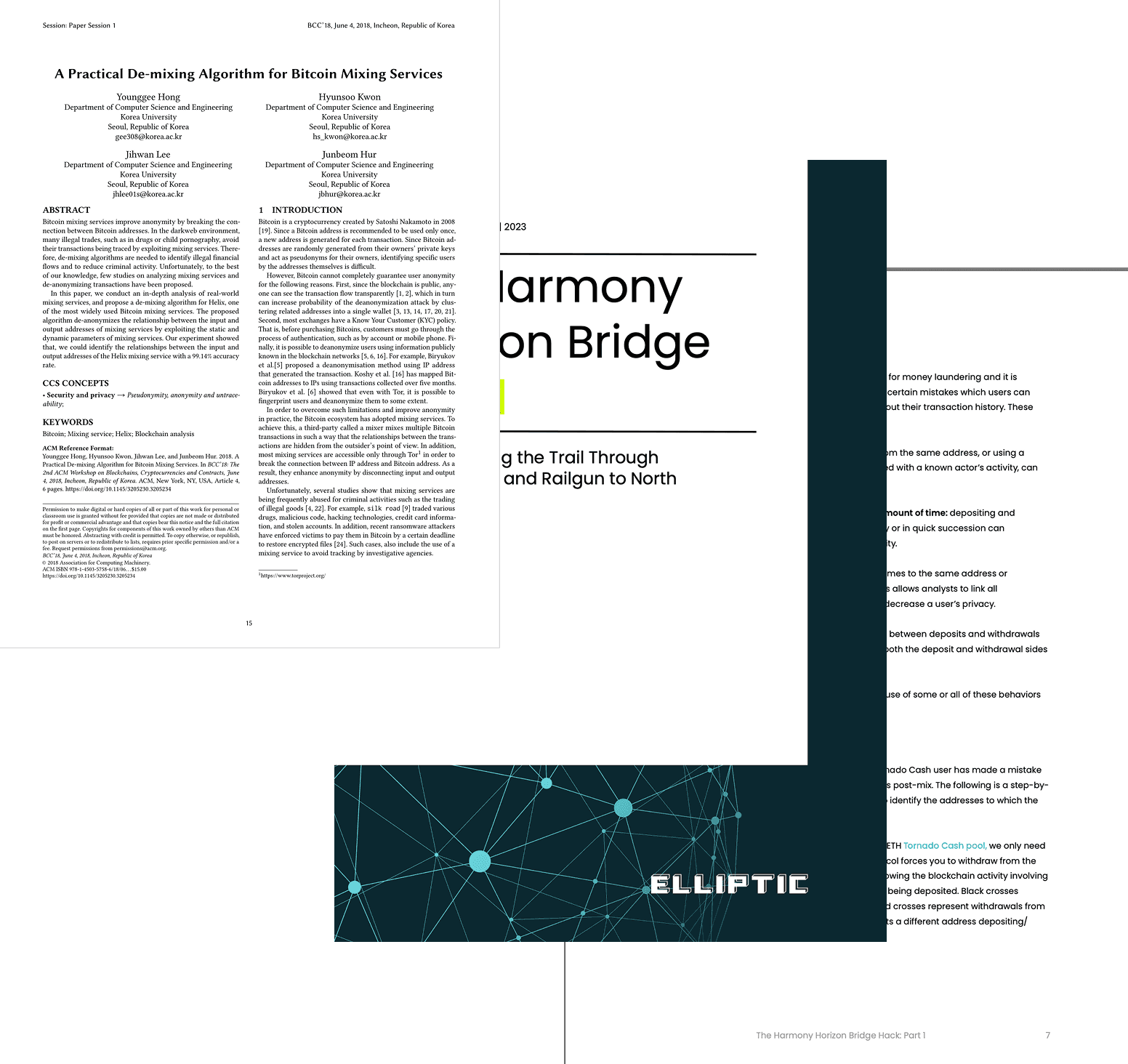
“We could identify the relationships between the input and output addresses (successfully demix) with 99.14% accuracy.”
—— Y. Hong, H. Kwon, J. Lee, and J. Hur, "A practical de-mixing algorithm for Bitcoin mixing services," in Proc. ACM Asia Conf. Comput. Commun. Secur. (AsiaCCS), 2018
"Although mixers can be very effective for money laundering and it is difficult to demix, there are certain human mistakes which can reveal parts of their transaction history."
—— Elliptic, "The Harmony Horizon Bridge Hack: Following the funds," Elliptic Connect, Jun. 24, 2022. [Online].
Assumption 4
Can we successfully correlate on-chain data to create a risk-scoring model for suspicious wallets?
Experiment: Interview with cryptocurrency analyst
Through technical consultations with industry experts, including a blockchain analyst and a lead blockchain engineer, we have evaluated specialized data providers to add a digital caller id to crypto accounts. This allows our tool to identify if an account is linked to suspicious activity.
We've been in the space since the early days, building our edge through extensive attribution data, private sources, and in-house cross-chain linking tools. These come from on-chain heuristics, paid providers, two-way exchange partnerships, and law-enforcement annotations."
Andy Chua
Cryptocurrency Intelligence Analyst @ Elliptic

Next steps
We will replicate researched methods that achieved 99% accuracy in linking hidden transactions. We will run a proof-of-concept using MetaSleuth's address label API and risk score API against known case addresses to measure entity label accuracy, and compare it against competing providers (Chainalysis, Elliptic, TRM Labs). We will fine tune our model until we can obtain a clear edge.
Legal landscape - Admissibility
Can we build an AI forensic tool that is admissible in court and liability-shielded?
Assumption | Experiment | Key takeaway | Next steps
Assumption 1
Can automated tracing and reports meet the evidentiary standards of courts?
Admissable criteria
Risk of failure
Sufficiently data to facilitate independent authentication
Judge may rule the resulting evidence inadmissible due to a lack of transparency
Application of AI in report synthesis does not compromise the accuracy of findings
GenAI models may inadvertently synthesize incorrect or hallucinate data points
Daubert Standard alignment so that Expert Witness can testify without software engineers
Court may mandate a deposition of the ninepointthree founders or lead engineers
Experiment: Expert interview
A walkthrough with a digital forensics expert witness to understand evidentiary standards required in court.
Interview with a paralegal and crypto scam investigators to identify the admissibility threshold for reports.
If the tool creates a reproducible timeline of the wallet activity before and after the theft, it satisfies the court’s need for a narrative."
"Someone needs to go through it, chatgpt can’t go the court themselves... there will be a lot of questions regarding the chain of evidences."

Basil Manoussos
Expert Witness (Digital Evidence) | Forensic Scientist | BCS Influence Board | Cyber Awareness Evangelist
Assumption 2
Can the business avoid liability and stay compliant?
Admissable criteria
Risk of failure
Our ToS and EULA are robust enough to protect ninepointthree against financial losses
Expensive backend maintenance as standards evolve faster than software development
Our platform maintains full alignment with global regulatory standards
Consumer protection laws in many regions can override limitation of liability clauses
Experiment: Expert interview
Consultations with crypto regulation experts, a corporate law trainee and a YC legal AI startup founder to verify a human in the loop statement would be sufficient to mitigate responsibility.
Assumption 3
Can we secure our competitive edge and prevent third-party infringement?
Admissable criteria
Risk of failure
Our research can be protected through a trade secret or patent
Inability to protect our research or maintain trade secret against replication by larger competitors
Our core assets are secured through copyright and trademarks.
Imitation of our visual identity & distinctive brand (risk to overall brand reputation)
Experiment: Expert interview
Consultation with Intellectual Property Patent Lawyers and with the IP patent office.

We talked with the intellectual property office directly. They gave us a referral for a consultation to verify our IP patentability.

Next steps
We will attend the IP office consultation and begin the patent process. In legal consultations, we will finalize our user data privacy policy. At later business stages, we will hire part and full time legal professional to provide compliance to support the founding team and strictly maintain our business reputation.
Risk assessment
Identifying our four key risks
Through the series of experiments, we have successfully de-risked the most critical assumption, ensuring our product is valuable to users, feasible to build, and legally compliant, and our stakeholders are reachable. To ensure total transparency and ongoing operational resilience, we maintain a database risk register tracking all remaining secondary and long-term risks.
Product roadmap
The 30-month horizon
To refine our product roadmap, ninepointthree consulted with the Imperial Enterprise Lab and examined industry standards to estimated the number of employees needed in different departments. We leveraged their 'Expert in Residence' program, participating in an Idea Surgery and working with a Business Coach to accelerate our development.

“Regulatory expertise is needed, you need to bring in legal and regulatory experts, potentially as contract hires, to make sure your evidence is actually usable in court.”
—— Imperial Enterprise Lab
“It took us two years with full-time developers to bring the initial open-source framework to production level. However, with LLMs, I believe this timeline will be significantly shorter, and prototyping even more so.”
“When hiring, we would not specify the candidate to have specific crypto knowledge, although computer science knowledge is essential.”
—— Michael Fröwis
Head of engineering @ Iknaio

Brand asset design to support competitive positioning
Our website, video and associated platforms (e.g. LinkedIn page) are intentionally designed to express our brand identity: an innovative newcomer ready to challenge and reshape a rapidly growing industry. The visual language and tone are both credible and forward-thinking, appealing directly to investigators seeking better tools as well as partners looking for high-potential opportunities. As we are targeting the US market, all our communications have been written in American English.
Special thanks to…
our community of sponsor users, experts and advisory partners for their continued support of ninepointthree’s mission.
Assumption 1 (High Risk)
Can we get access to on-chain transaction data?